Kali Linux is like a toolbox filled with all the tools you need for digital adventures, and when you pair it with a Raspberry Pi, it’s like wielding those tools on a compact, versatile Swiss Army knife. In this article, we will dive into the fascinating world of Kali Linux and explore how it can empower your Raspberry Pi projects. Whether you’re a tech enthusiast, a cybersecurity hobbyist, or just someone looking to supercharge your Raspberry Pi, you’ve come to the right place.
What is Kali Linux?
An Introduction to Kali Linux
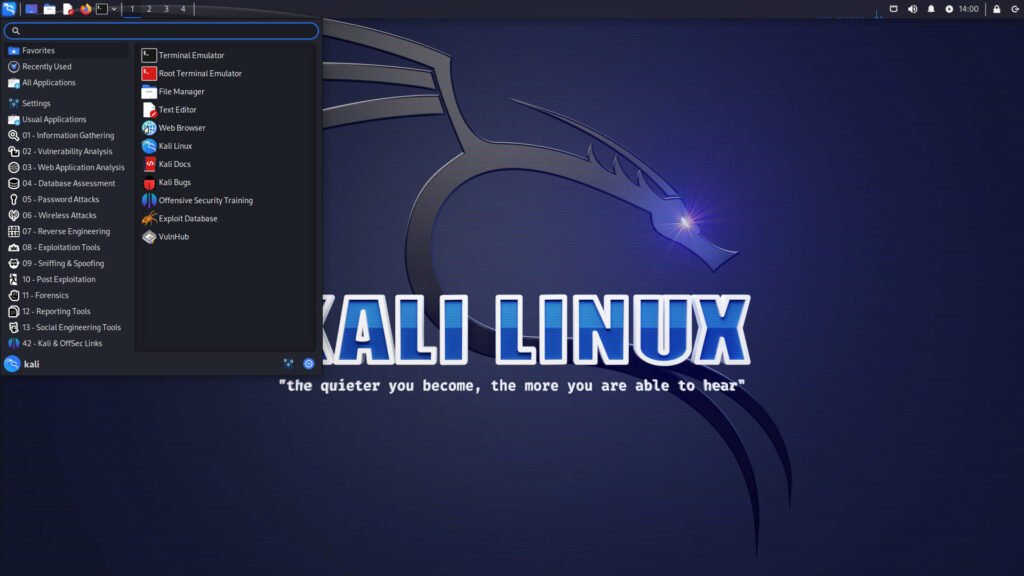
Kali Linux is a powerful, Debian-based Linux distribution designed for digital forensics, penetration testing, and security auditing. It’s like having a super-sleuth on your computer, ready to uncover hidden vulnerabilities and ensure your digital world is secure. Kali Linux comes equipped with a vast collection of cybersecurity tools, making it a favorite among professionals and enthusiasts alike.
Kali Linux stands out because it’s open-source, constantly updated, and backed by a vibrant community. But how does it relate to our trusty Raspberry Pi?
Why Raspberry Pi?
The Perfect Match: Raspberry Pi and Kali Linux
Raspberry Pi, often referred to as a tiny, credit-card-sized computer, is known for its versatility. It’s a marvel of technology that fits in the palm of your hand. But the real magic happens when you combine the Raspberry Pi with Kali Linux.
Think of Kali Linux as the superhero suit and Raspberry Pi as the wearable tech. This combination allows you to take your projects to the next level, whether it’s about cybersecurity, programming, or just tinkering with technology.
Setting Up Kali Linux on Raspberry Pi
A Step-by-Step Guide
The process of setting up Kali Linux on your Raspberry Pi is relatively straightforward. Here’s a simplified guide:
- Get the Necessary Hardware: You’ll need a Raspberry Pi board, a microSD card, a power supply, and an internet connection.
- Download Kali Linux: Visit the official Kali Linux website, download the Raspberry Pi image, and flash it to your microSD card.
- Boot Up: Insert the microSD card into your Raspberry Pi, connect it to your monitor, keyboard, and mouse. Power it up!
- Initial Configuration: Follow the on-screen prompts to set up your Kali Linux environment.
- Update and Upgrade: Once you’re in, run the commands
sudo apt updateandsudo apt upgradeto keep your system up to date.
With these simple steps, you’ll have Kali Linux up and running on your Raspberry Pi.
Getting to Know Kali Linux Tools
Discover the Arsenal
Kali Linux is renowned for its arsenal of tools, including but not limited to Wireshark, Metasploit, Nmap, and Burp Suite. These tools serve various purposes, from network analysis and penetration testing to web security and ethical hacking.
Let’s briefly explore a few key tools:
- Wireshark: A powerful network protocol analyzer that helps you inspect data from a live network or a capture file.
- Metasploit: The go-to tool for penetration testers, it aids in finding, verifying, and exploiting vulnerabilities.
- Nmap: A versatile network scanning tool that reveals open ports, services, and other valuable information.
- Burp Suite: Essential for web application security, it can help identify and fix security issues in your web applications.
Kali Linux equips you with these and many more tools, giving you the power to understand and secure your digital environment.
Kali Linux for Cybersecurity Enthusiasts
Enhancing Your Security Game
Are you concerned about the safety of your digital assets? Kali Linux can be your best friend in the world of cybersecurity. Whether you’re a professional or a beginner, this powerful Linux distribution has something to offer.
Kali Linux allows you to:
- Conduct Vulnerability Assessments: Identify weak spots in your network or applications before cybercriminals do.
- Perform Penetration Testing: Ethically hack your systems to find vulnerabilities and fix them.
- Explore Digital Forensics: Use Kali Linux to investigate incidents, recover data, and understand what went wrong.
Kali Linux transforms you into a digital Sherlock Holmes, ready to unravel the mysteries of the cyber world.
Kali Linux for Ethical Hacking
Exploring the World of White Hat Hacking
Ethical hacking, also known as white hat hacking, involves using hacking skills for good. Kali Linux is the primary choice for ethical hackers due to its vast toolkit. Whether you’re learning the ropes or a seasoned professional, Kali Linux offers the tools and resources you need to succeed.
Some key areas in ethical hacking with Kali Linux include:
- Password Cracking: Test the strength of your passwords and protect your accounts.
- Wireless Network Security: Audit and secure your Wi-Fi network.
- Social Engineering: Learn how to recognize and defend against social engineering attacks.
- Web Application Security: Find and fix vulnerabilities in your web applications.
Kali Linux provides a safe playground for ethical hackers to sharpen their skills and protect against malicious intruders.
Kali Linux for Network Testing
Diagnosing and Optimizing Networks
Network professionals and enthusiasts can benefit greatly from Kali Linux. Its tools can help you diagnose network issues, optimize performance, and ensure the security of your systems.
Some network-related tasks you can accomplish with Kali Linux include:
- Network Scanning: Discover devices on your network and identify potential security risks.
- Packet Analysis: Examine data packets to troubleshoot network issues.
- Firewall Testing: Assess the effectiveness of your network’s security measures.
- Wi-Fi Hacking Prevention: Learn how to secure your wireless networks against unauthorized access.
Kali Linux is a treasure trove for network administrators, offering the right tools for maintaining a robust and secure network.
Kali Linux for Web Security
Keeping Your Online Presence Safe
In an era where online threats are ever-present, web security is of paramount importance. Kali Linux aids web developers, administrators, and security professionals in safeguarding web applications and websites.
Kali Linux empowers you to:
- Scan for Vulnerabilities: Identify weaknesses in web applications and websites before malicious actors do.
- SQL Injection Testing: Test your databases for vulnerabilities and prevent data breaches.
- Cross-Site Scripting (XSS) Testing: Detect and eliminate XSS vulnerabilities that can compromise your users’ data.
- Web Server Security: Ensure your web servers are hardened against attacks.
By using Kali Linux, you can be proactive in securing your online presence, protecting your reputation, and ensuring your users’ trust.
Kali Linux for Penetration Testing
Strengthening Your Digital Defenses
Penetration testing, often referred to as pen-testing, is a crucial component of cybersecurity. It involves simulating cyberattacks to identify vulnerabilities in your systems. Kali Linux is the ultimate tool for penetration testers.
Kali Linux assists in:
- Identifying Weaknesses: Discover vulnerabilities that malicious actors could exploit.
- Exploiting Vulnerabilities: Test your systems’ resilience against attacks.
- Reporting and Remediation: Provide actionable insights for fixing identified issues.
- Staying One Step Ahead: Keep up with the latest threats and defense strategies.
With Kali Linux, you’re well-equipped to safeguard your digital assets and stay ahead in the ever-evolving landscape of cybersecurity.
Projects and Fun with Kali Linux on Raspberry Pi
Unleash Your Creativity
Kali Linux isn’t just for professionals and security enthusiasts; it’s also a fantastic platform for creative projects. Here are a few ideas to spark your imagination:
- Raspberry Pi Cybersecurity Device: Transform your Raspberry Pi into a portable, dedicated cybersecurity tool.
- Home Network Security: Protect your home network with Kali Linux and Raspberry Pi.
- Programming and Development: Use Kali Linux for programming, web development, and software testing.
- IoT Security: Secure your Internet of Things (IoT) devices using Kali Linux and Raspberry Pi.
With Kali Linux and Raspberry Pi, the possibilities are endless, and your creativity knows no bounds.
Conclusion
Uniting Kali Linux and Raspberry Pi: A Powerful Duo
In conclusion, Kali Linux and Raspberry Pi make an unbeatable combination. Whether you’re exploring the realms of cybersecurity, ethical hacking, network testing, or just having fun with creative projects, these two technologies are here to empower you.
By following this guide, you can dive into the exciting world of Kali Linux on Raspberry Pi. You’ll have a secure, versatile, and highly customizable platform at your disposal. The only limit is your imagination.
So, what are you waiting for? Embrace the power of Kali Linux on Raspberry Pi and embark on your digital adventures today!
Frequently Asked Questions (FAQs)
What is Kali Linux?
Kali Linux is a Debian-based Linux distribution designed for digital forensics, penetration testing, and security auditing. It’s packed with cybersecurity tools to help professionals and enthusiasts uncover vulnerabilities and ensure digital security.
How can I set up Kali Linux on Raspberry Pi?
Setting up Kali Linux on Raspberry Pi involves getting the necessary hardware, downloading the Kali Linux image, flashing it to a microSD card, and configuring the system. Once done, you’ll have Kali Linux up and running on your Raspberry Pi.
What are some key tools in Kali Linux?
Kali Linux includes a wide array of tools, such as Wireshark, Metasploit, Nmap, and Burp Suite, used for network analysis, penetration testing, and web security, among other purposes.
Can Kali Linux help with cybersecurity?
Absolutely. Kali Linux is a powerful tool for cybersecurity enthusiasts. It enables vulnerability assessments, penetration testing, and digital forensics, helping you protect your digital assets.
Is Kali Linux suitable for ethical hacking?
Yes, Kali Linux is a preferred choice for ethical hackers. It offers tools for password cracking, wireless network security, social engineering defense, and web application security, allowing ethical hackers to strengthen their skills and protect against malicious intruders.